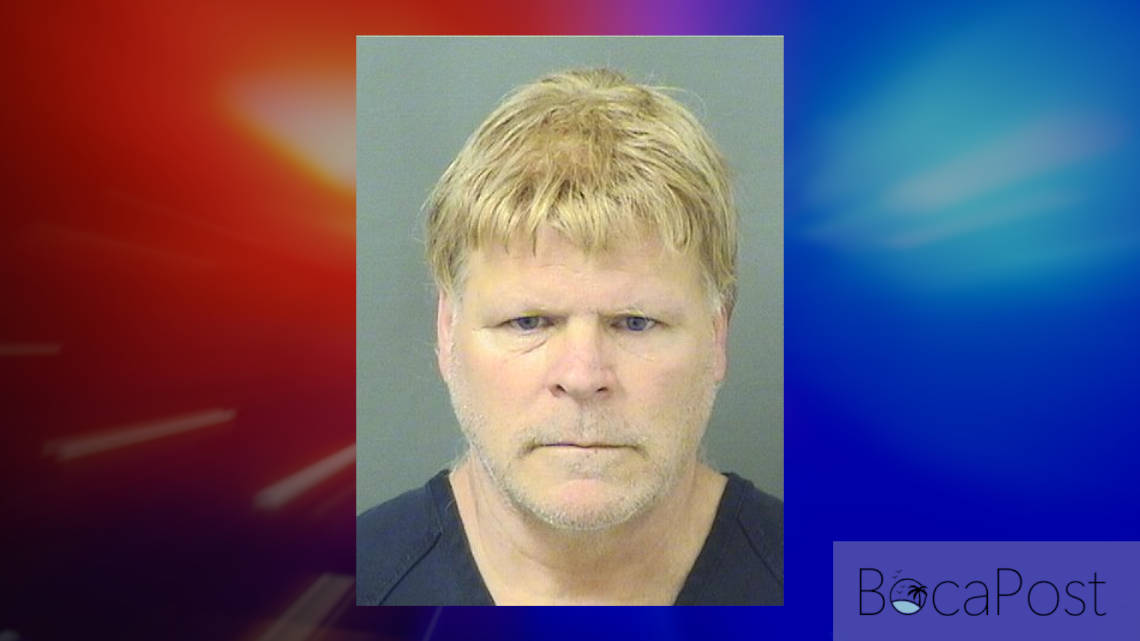
Valet At The Boca Raton Resort Arrested For Possession Of Obscene Material
Jonathan Schrift Charged With 25 Counts Of Possession Of Child ****. Schrift Worked Full Time As A Valet At The Boca Raton.

Valet At The Boca Raton Resort Arrested For Possession Of Child ****
BOCA RATON, FL (Boca Post) — A man who reportedly lives at Boca Raton’s Boca Inn was arrested on 25 counts of possession of child ****, according to jail records released to Boca Post by the Palm Beach County Sheriff’s Office.
Jonathan Schrift, 38, who reportedly lives at Boca Raton’s Boca Inn located at 1801 N. Federal Highway in Boca Raton, has been arrested Friday afternoon by the Lantana Police Department. Boca Post has been notified that Schrift has been charged with 25 counts of “827.071(5) POSSESSION OF SEXUAL PERFORMANCE BY A CHILD”.
Schrift was booked into the Palm Beach County Jail at 3:21 on Friday afternoon where he remains today with a bond set at $75,000.
Note, according to Schrift’s arrest paperwork, “1801 N FEDERAL HWY 117, BOCA RATON, FL 33432” is listed as his residence. That is the address of the “Boca Inn” in East Boca.
Police say that Schrift worked as a valet person at the Boca Raton Resort located at 501 E Camino Real in Boca Raton, FL.
Lantana Police Department tells Boca Post that Schrift’s arrest was the result of a 6-month investigation that originated from an NCMEC (National Center for Missing and Exploited Children) Cyber Tip.
Lantana Police provided Boca Post with the following statement:
This case is the result of an approximately 6-month-long investigation by Det Gibson of the Lantana Police Departments Detective Bureau after a CYBERTIP was received by NCMEC (National Center for Missing and Exploited Children) which resulted in the arrest of W/M Jonathan Schrift (DOB 12/14/1983) who was residing within the jurisdiction of the Lantana Police Dept, however, moved during the course of the investigation to the Boca Inn located at 1801 N Federal Hwy Room 117 Boca Raton, FL 33462. Schrift was found to be in possession of hundreds of images and videos depicting Child ****. Although Schrift has been arrested this case remains ongoing at this time.
The following is the narrative of the official arrest affidavit submitted by the Lantana Police Department:
-
- On January 24, 2022, Your Affiant was assigned NCMEC CYBERTIP# 109226192 via the ICAC PORTAL. Your Affiant then reviewed the details of the CYBERTIP which advised the reporting electronic service provider (ESP) was YAHOO (Oath Holdings Inc) “herein referred to as YAHOO”. YAHOO reported the incident type was Child **** (possession, manufacture, distribution). YAHOO reported that the incident time was 11~30-2021 12:07:34 UTC which is the date and time when YAHOO submitted the CYBERTIP to NCMEC.
- CyberTips are investigative leads generated by the National Center for Missing and Exploited Children (NCMEC). NCMEC is a non-profit organization that provides services nationwide for families and professionals in the prevention of abducted, endangered and sexually exploited children. Pursuant to its mission and its congressional authorization (former 42 USC § 5773, now 34 USC § 11293)) NCMEC operates the CyberTip line and Child Victim Identification Programs to assist law enforcement in identifying victims of child **** and child sexual exploitation. NCMEC works with law enforcement, Internet Service Providers, electronic payment service providers, and others to reduce the distribution of child sexual exploitation images and videos over the Internet. NCMEC forwards reports of child sexual exploitation to law enforcement for the purposes of investigation and disposition.
- Under 18 U.S.C. § 2258a (2008), any electronic communication service provider that obtains actual knowledge of any facts or circumstances from which a violation of federal child **** laws is apparent must report the facts and circumstances to the Cyber Tip Line at NCMEC. NCMEC then forwards the reported information to both state and federal law enforcement officials. 18 U.S.C. § 2258c. An internet service provider that fails to report such facts is subject to significant fines. 18 U.S.C. § 2258e.
- Your Affiant and the South Florida ICAC have received many Cyber Tips while assigned to the task force, and although not every tip resulted in an arrest, the information contained within the tips was found to be accurate and reliable. In Woldridge v. State, 958 So.2d 455 (2d DCA 2007), the court held that an ISP acting in compliance with the federal reporting law has a presumption of reliability akin to that afforded a citizen informant.
- Your Affiant knows from training and professional experience that when NCMEC advises that there was a hash value match for a file, and it is classified as apparent child ****, it means that NCMEC and either an ESP, or law enforcement agency, (all of whom have a statutory duty to report child abuse) previously had an employee or officer open the file and confirm that this exact same file was apparent child ****.
- The original report to NCMEC was made by the ESP YAHOO. YAHOO is a social networking website and phone application that allows individuals on the internet to communicate with one another on a stationary or mobile electronic device. On YAHOO, you also have the ability to upload pictures and videos that are stored on your digital devices. ESP’s sometimes uses hash value algorithm software like Microsoft Photo DNA and user reports to report child sexual abuse material to NCMEC. They are also under a statutory duty to report it when they become aware of a file that is child ****, and they classify it accordingly. In this case, YAHOO reported the uploaded/shared video/image file to NCMEC as Child ****, at which time NCMEC did view some of the uploaded files which were determined to contain apparent child ****. YAHOO reported that it did view the ENTIRE contents of some of the uploaded files which they also confirmed that it contained apparent child ****. The above information reported by the ESP YAHOO and the NCMEC report leads Your Affiant to have probable cause that these files also would contain child ****.
NOTED: A prior CYBERTIP (127540) was submitted by a member of the public, appears related, and was made available to the Illinois Lake County Sheriff’s Office Investigator Hobbs in 2003. CI/TA results for “b96jon”, however when Lake County Sheriff’s Office was contacted it appears as though that case was never followed up on.
-
- YAHOO provided 88 files dating from 2005 through 2020 that the suspect account had yn} Uploaded and downloaded confirmed child **** using his [email protected] and his tj alternate listed and verified jonschrift1983gqmail.com accounts. These accounts were also used to send confirmed child **** to other recipients as well. 9. Your Affiant then downloaded all 88 case files (with approximately 80 or more all containing confirmed child ****) with the following just being several of the files that the suspect uploaded/shared:
Boca Post redacted the titles and descriptions of the files due to their graphic nature. The report lists files with graphic descriptions of underage boys.
-
- Due to your affiant’s training knowledge and experience, when the word “Verified” appears after a given email address or telephone number that indicates that a 2-step verification process took place where a message was sent to those specific places, whereas the suspect would have to respond back to them to verify that they are the actual account holder of that specific email address and telephone number that was provided for registration.
- On January 25, 2022 preservation requests were sent to YAHOO to preserve the user account [email protected], and GOOGLE to preserve the user account [email protected]
- On January 25, 2022 subpoenas were obtained and later executed with responses being received for the following: T-Mobile telephone number 847-275-4915 (belongs to David Brocato to an address in IL) ATT telephone number 312-282-8475 (belongs to suspect Jonathan Schrift to an address in IL) Honix Corporation for IP address 2607:££28:9007:1::53e8 used on 11-28-2021 at 03:17:31 urc (The only info provided from the subpoena was that it belongs to a VPN provider PANGO Inc which offers private/secure and encrypted web browsing with the registration to the service bei created on 7/30/2019 and the last login to the above IPV6 was from IPV4 201.202.164.42 on 1/10/22 1519hrs, at which time I performed an open-source search of that IPV4 which came back to COSTA RICA. I then contacted PANGO to find out where to send a subpoena, and they responded that they would not be able to provide any specific use due to the VPN service they provide).
- A records check was performed in the FLORIDA DRIVER AND VEHICLE INFORMATION DATABASE which revealed the following suspect information: Name: Jonathan Schrift (DOB 12/14/1983) Address: 115 N 12th St Lantana, FL 33462 Sst: FL DL# S613-428-83-454-0
- The FLORIDA DRIVER AND VEHICLE INFORMATION DATABASE also advised that Schrift was born in IL and was issued his FL DL at that specified address within the jurisdiction of the Lantana Police Dept on 6/11/20 which was prior to the last uploaded video depicting confirmed child **** on 12/1/2020.
- It was also discovered that on 8/21/2020 the suspect reported to the Lantana Police Dept that his Credit Card was fraudulently used where he provided the telephone number 312-282-8475 which was also the same telephone number provided in the CYBERTIP by the ESP YAHOO as being linked to the two above aforementioned email addresses.
- A search warrant for the suspect’s YAHOO account was obtained and executed with a response is later received. Upon reviewing the data, it revealed the account does belong to the suspect. There were numerous communications where the suspect identified himself as Jonathan Schrift and his address was 115 N 12th St Lantana, FL 33462. Pictures were also discovered of the suspect where he was positively identified by his FL DL as Jonathan Schrift (DOB 12/14/1983). Also discovered were several of the above aforementioned CYBERTIP files containing CONFIRMED CHILD ****. The content was dated 6/9/2005 through 11/29/2021 showing the suspect had continuous possession of that account during that timeframe and continuous access to the illegal material (this account was deactivated by YAHOO upon reporting of the CYBERTIP).
- A search warrant for the suspect’s GOOGLE account was obtained and executed with a response is later received. Upon reviewing the data, it revealed the account. does belong to the suspect. There were numerous communications where the suspect identified himself as Jonathan Schrift and his address was 115 N 12th St Lantana, FL 33462. Pictures were also discovered of the suspect Jonathan Schrift who was positively identified by his FL DL. Within the account, multiple pictures of the suspect’s Florida and previous Illinois driver’s licenses were located. There were also screenshots from a cell phone payment sent from the suspect and the address 115 N 12th St Lantana, FL 33462. Also discovered within the suspect’s GOOGLE account were dozens and dozens of files containing INFIRMED CHILD ****. The content was dated from 10/8/2008 through 1/27/2022 showing the suspect had continuous possession of that account during the timeframe and continuous access to the illegal material (this account is believed to be still active due to the non-disclosure in the search warrant). Within this GOOGLE ACCOUNT, the vast majority (well beyond a hundred videos and images) of confirmed child ****was located within the suspect’s GOOGLE PHOTOS. GOOGLE PHOTOS stores your photos and videos in “the cloud” – this is just tech-talk for online storage. GOOGLE PHOTOS can also be stored on specific devices or computers that connect to the internet before being saved to the cloud. Google photos can also be backed up to any device capable of electronic storage and can be viewed without having internet access. Once saved to the CLOUD the videos or images can be accessed from anywhere and any device that can access the internet.
- Since this investigation began the suspect has moved from his residence located at 115 N 12th St Lantana, FL 33462 to another location.
- A wage and hour report was requested by your Affiant which revealed that he currently is working for SP PLUS, which is a baggage and valet service provided to businesses throughout the country.
- Through this investigation, it has been discovered the suspect was currently working as a valet at the Boca Resort and Club located at 501 E Camino Real Boca Raton, FL 33432. A subpoena was then obtained and executed to SP PLUS which confirmed his employment at that location as a full-time valet. Surveillance was conducted at which time the suspect was positively identified and observed working on the property.
- Through this investigation, the suspect was found to be residing at the Boca Inn ROOM #117 located at 1801 N Federal Hwy Boca Raton, FL 33462 at which time surveillance was conducted where the suspect was positively identified and observed exiting that motel room daily during that time frame. The suspect was observed leaving that room carrying on his back a large dark-colored backpack. No other subject was observed coming from the room.
- A lawful search warrant for the Boca Inn 1801 N Federal Hwy #117 Boca Raton, FL 33432 was granted as well as a search warrant for his persons.
- On 7/1/22 the search warrants were executed with the assistance of Boca Raton PD and the Dept of Homeland Security, where Schrift was detained as he exited his room. The SW of the room revealed a black Samsung phone on his bed as well as a black tablet. DHS assisted with the searching of the devices which revealed in well in excess of 25 videos and images depicting Child **** on that phone. The tablet did not reveal illegal material.
- Schrift has then transported back to the Lantana Police Dept where the search warrant for his person was executed. (1) cracked phone was located as well as another (1) black Samsung phone was located within his backpack with forensic exams still being conducted.
- An interview was then conducted with Miranda Warnings being ready. Post Miranda Schrift stated that the GOOGLE and YAHOO account did belong to him as well as the phone seized off his bed. Schrift stated that he obtained the material from online sites and at first, believed the subjects to be 18yoa and older. Schrift later stated that he did believe a good majority of the videos and images to be that of minors.
- At this, I find probable cause exists that arrest and charge Schrift with 25 counts of possession of Child ****. Schrift was then transported to PBCJ without incident.